Nexus Website — Complete Market Infrastructure Overview
What Makes the Nexus Darknet Platform Distinct?
The Nexus Website documents one of the most architecturally sophisticated darknet marketplace platforms operating on the Tor network. The Nexus darknet infrastructure combines multi-signature escrow, rotating mirror addresses, and a tiered vendor trust system — features that distinguish it from earlier-generation markets that relied on centralised escrow or single-point access addresses.
Unlike platforms that emerged as simple listing directories, Nexus was designed with adversarial threat modelling from inception. Its vendor onboarding pipeline, communication encryption standards, and buyer protection mechanisms reflect documented lessons from the operational failures of prior darknet markets. For official access, see the official Nexus access links.
Publicly available research, including reports from Chainalysis, DarkOwl, and various academic institutions, has referenced Nexus as a case study in resilient marketplace design. The platform's sustained uptime through periods of intense law enforcement activity has attracted significant researcher and journalist attention since its emergence.
- Decentralised escrow — no single administrator holds funds
- Vendor bonding reduces financial incentive for fraud
- Rotating .onion addresses maintain consistent availability
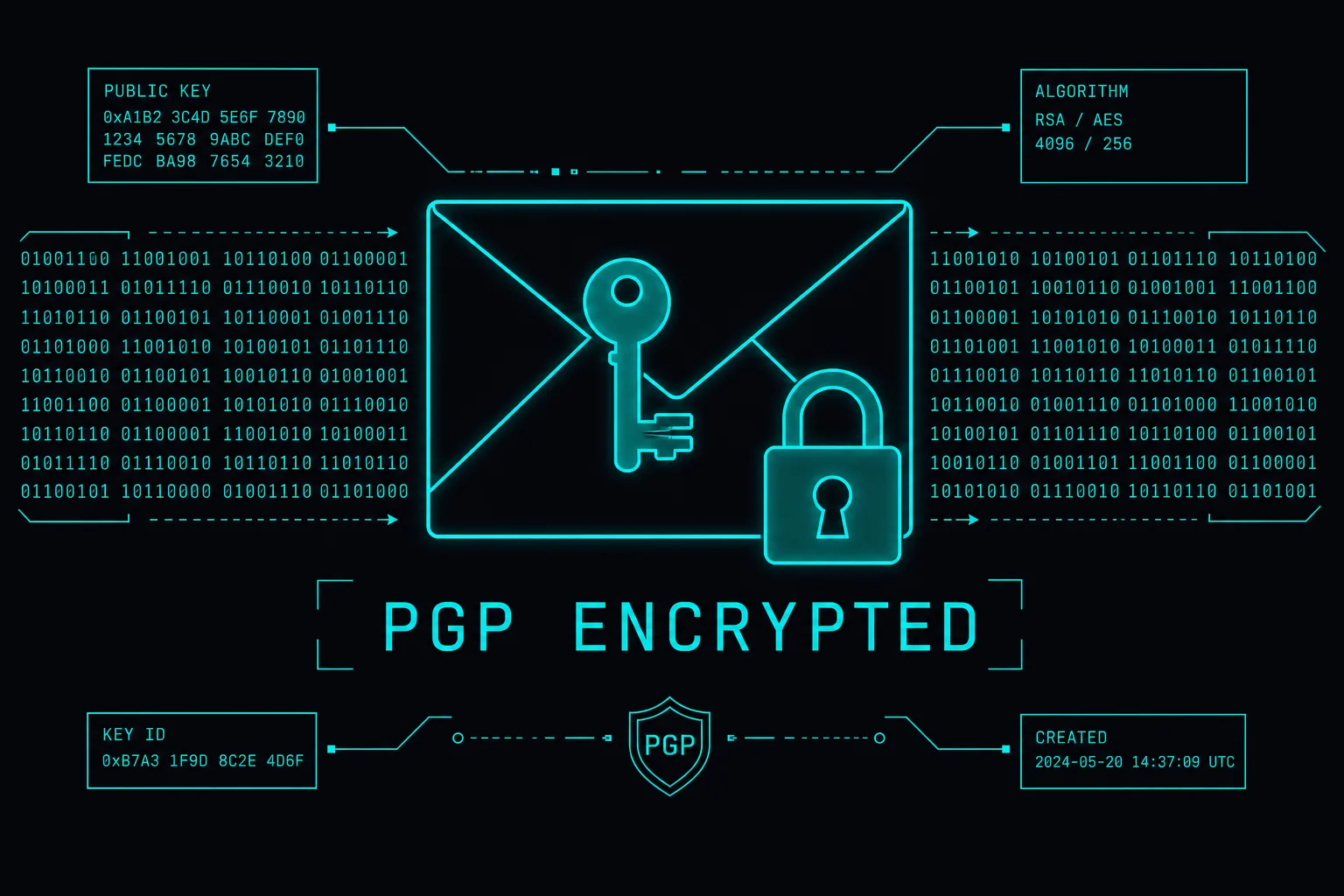
- PGP mandatory at account level — not optional
- Buyer review system is cryptographically tamper-resistant
Nexus Verified Vendor Infrastructure: 12 Core Pillars
The following twelve components represent the architectural foundation of the Nexus platform as documented through publicly available sources, market research, and community-sourced analysis. The Nexus Verified designation ties directly to several of these pillars.
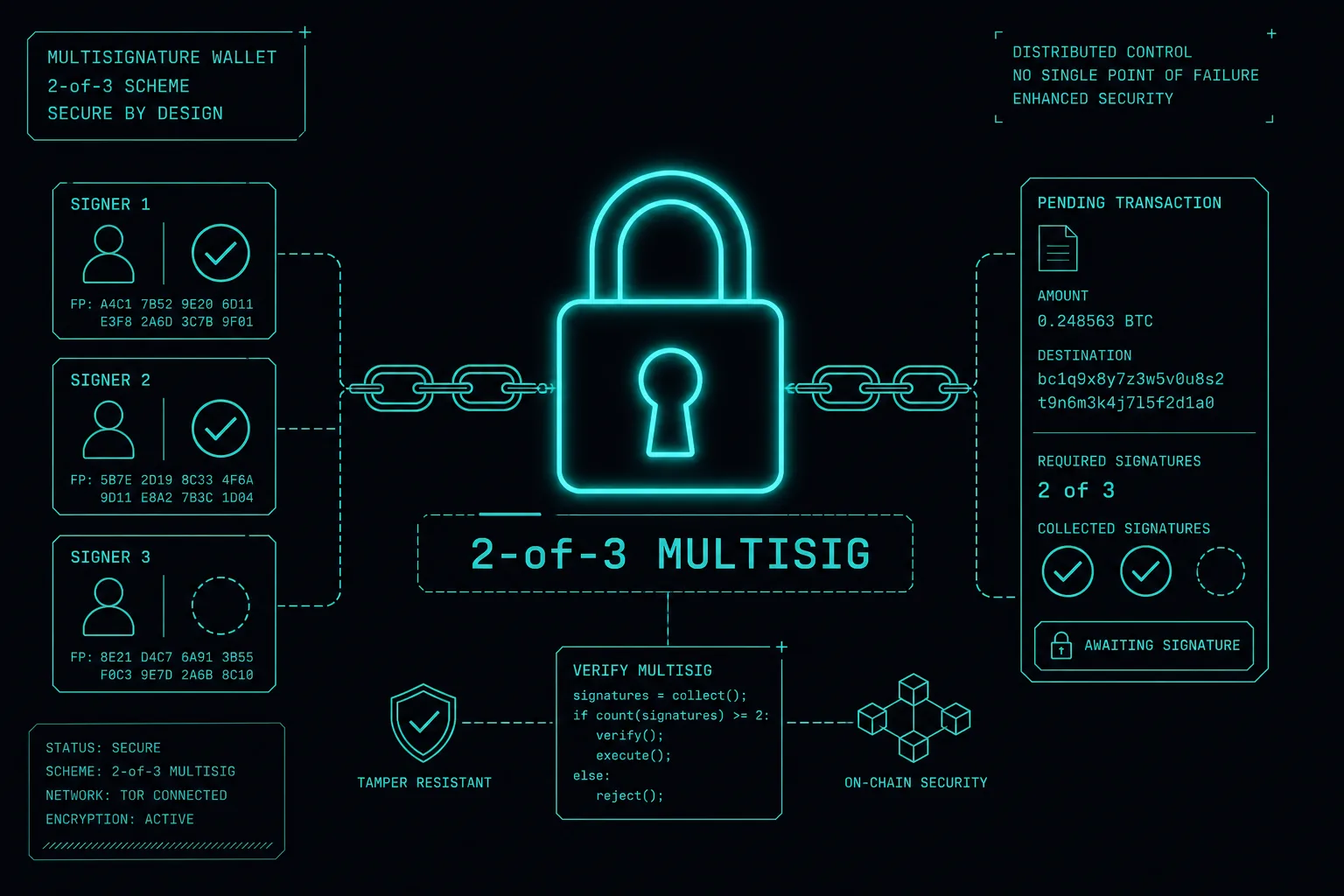
01 — Multi-Sig Escrow
Nexus operates a 2-of-3 multi-signature Bitcoin escrow. Funds are locked until two of three parties (buyer, vendor, platform) sign release. This eliminates exit scam risk from either side unilaterally accessing funds.

02 — Vendor Bonding
New vendors pay a refundable bond before gaining access to the listing system. The bond amount scales with listing category risk level. This financial commitment reduces the number of low-effort or fraudulent vendor applications.
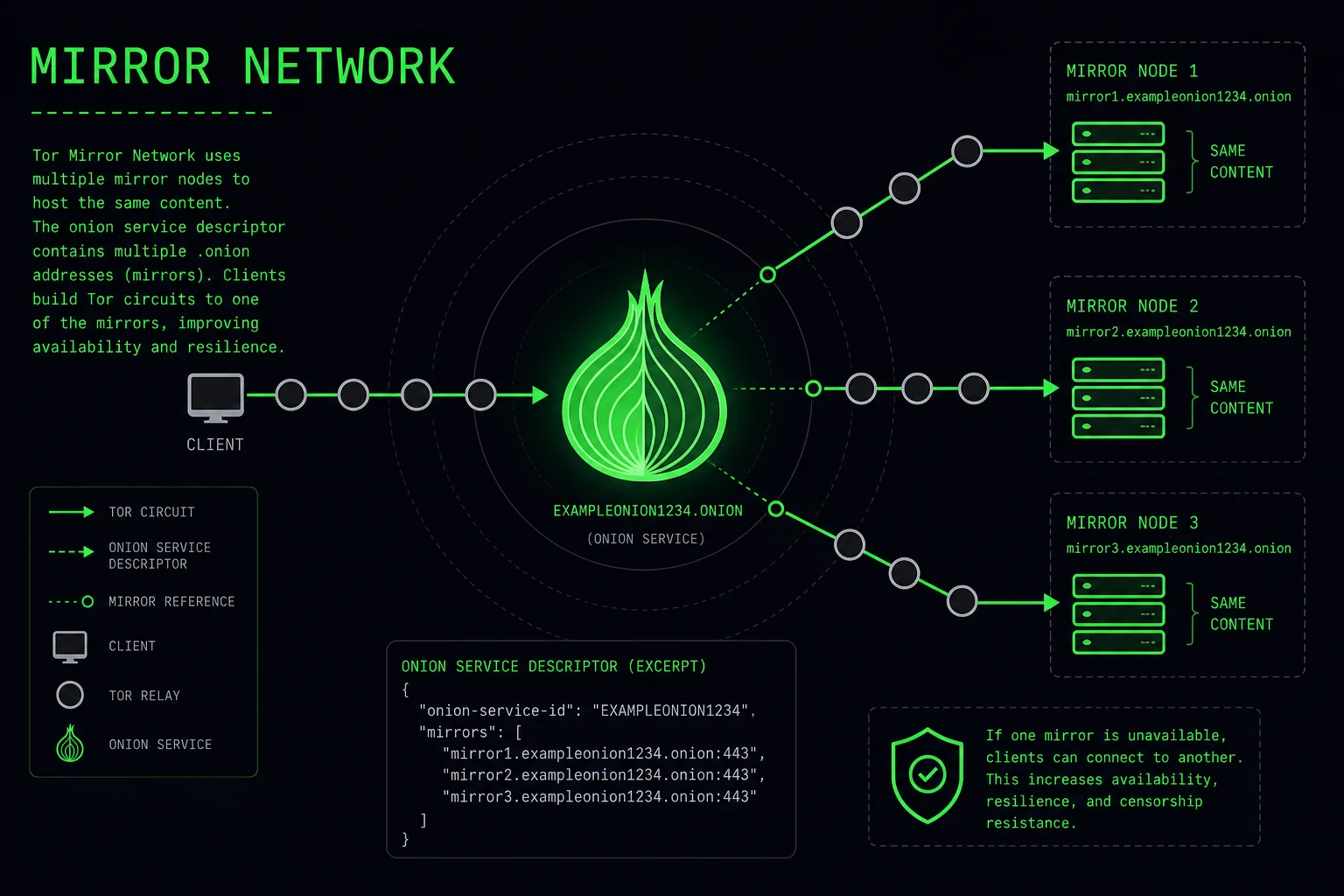
03 — Mirror Network
Three active .onion mirrors rotate on a 72-hour cycle. Each address is cryptographically signed in the platform's PGP-verified address publication. Mirror rotation limits the exposure window for any single address if targeted.
04 — Dispute Resolution
A dedicated resolution team handles escrow disputes. Cases are evaluated on order evidence, messaging logs, tracking data, and vendor history. The median resolution window is 18–24 hours for standard category disputes.
05 — Mandatory PGP
PGP encryption is enforced platform-wide. Vendors register public keys at account creation. All order communications containing shipping details must be PGP-encrypted before transmission. The platform validates key integrity at each session.
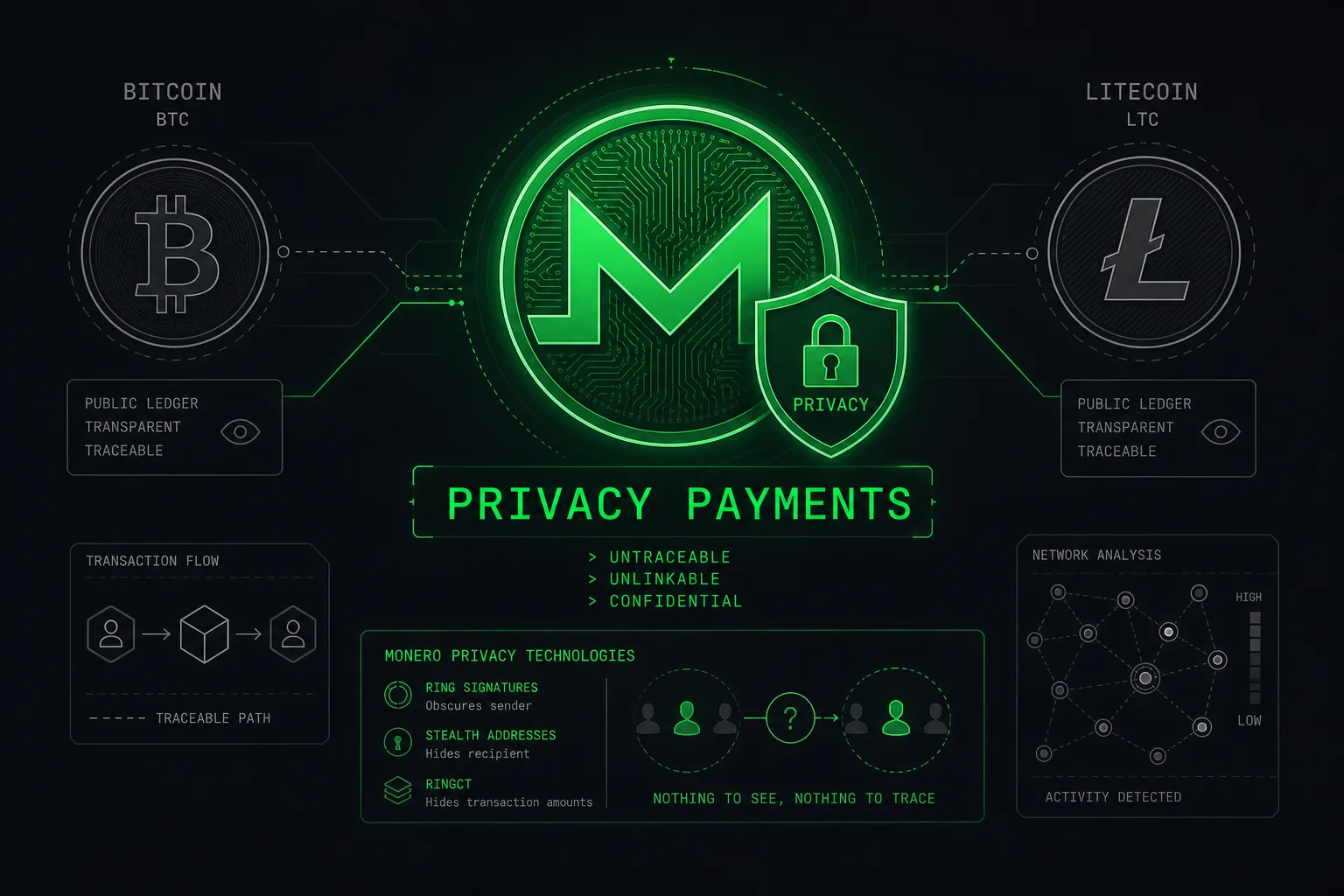
06 — Crypto Rails
Native support for BTC, LTC, and XMR is built into the transaction layer. XMR is the default-recommended option. The platform's internal wallet system generates fresh deposit addresses per transaction to prevent blockchain correlation.
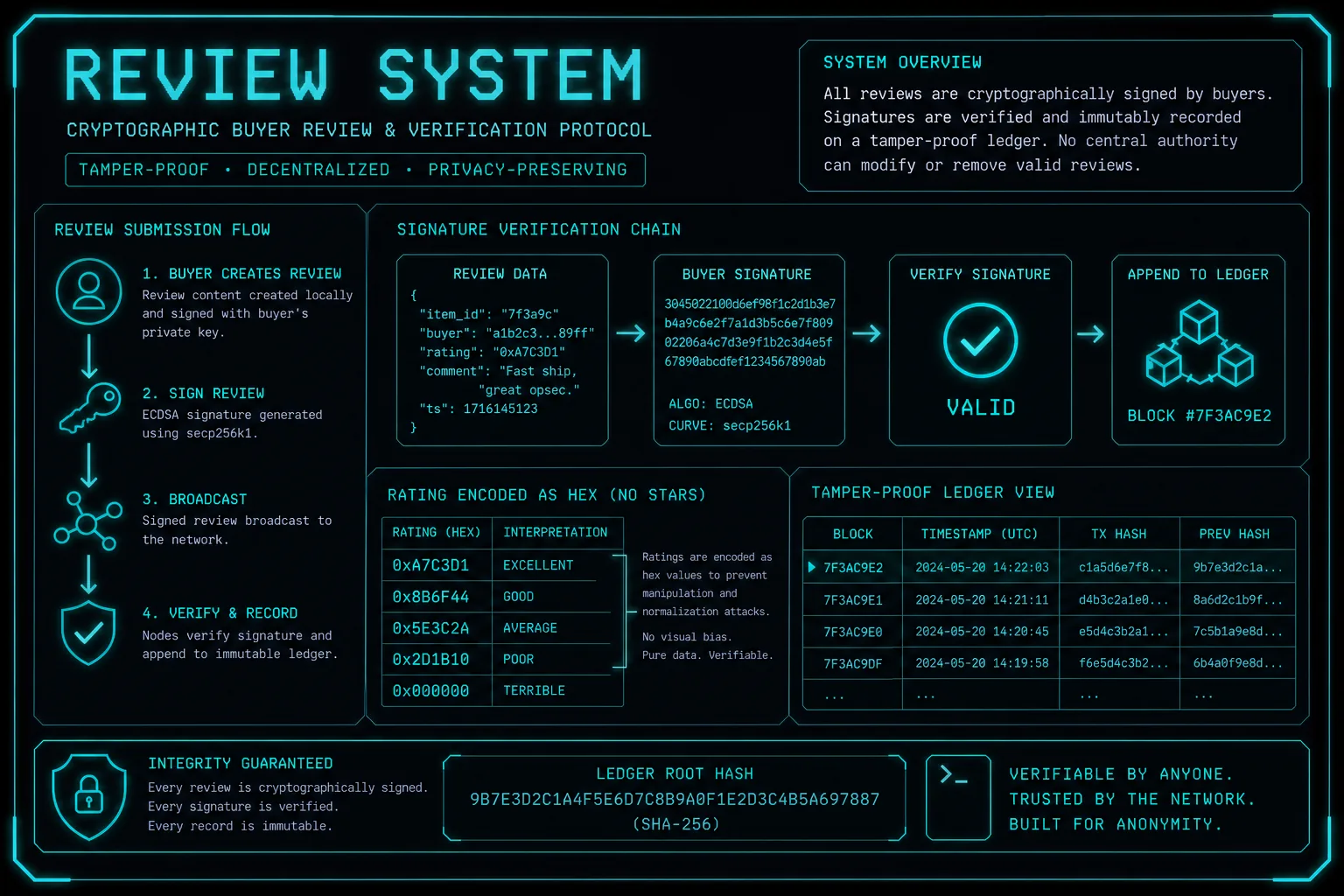
07 — Signed Reviews
Buyer reviews are cryptographically signed with session tokens tied to completed order identifiers. This prevents vendors from self-reviewing, purchasing fake feedback, or manipulating their displayed trust scores.
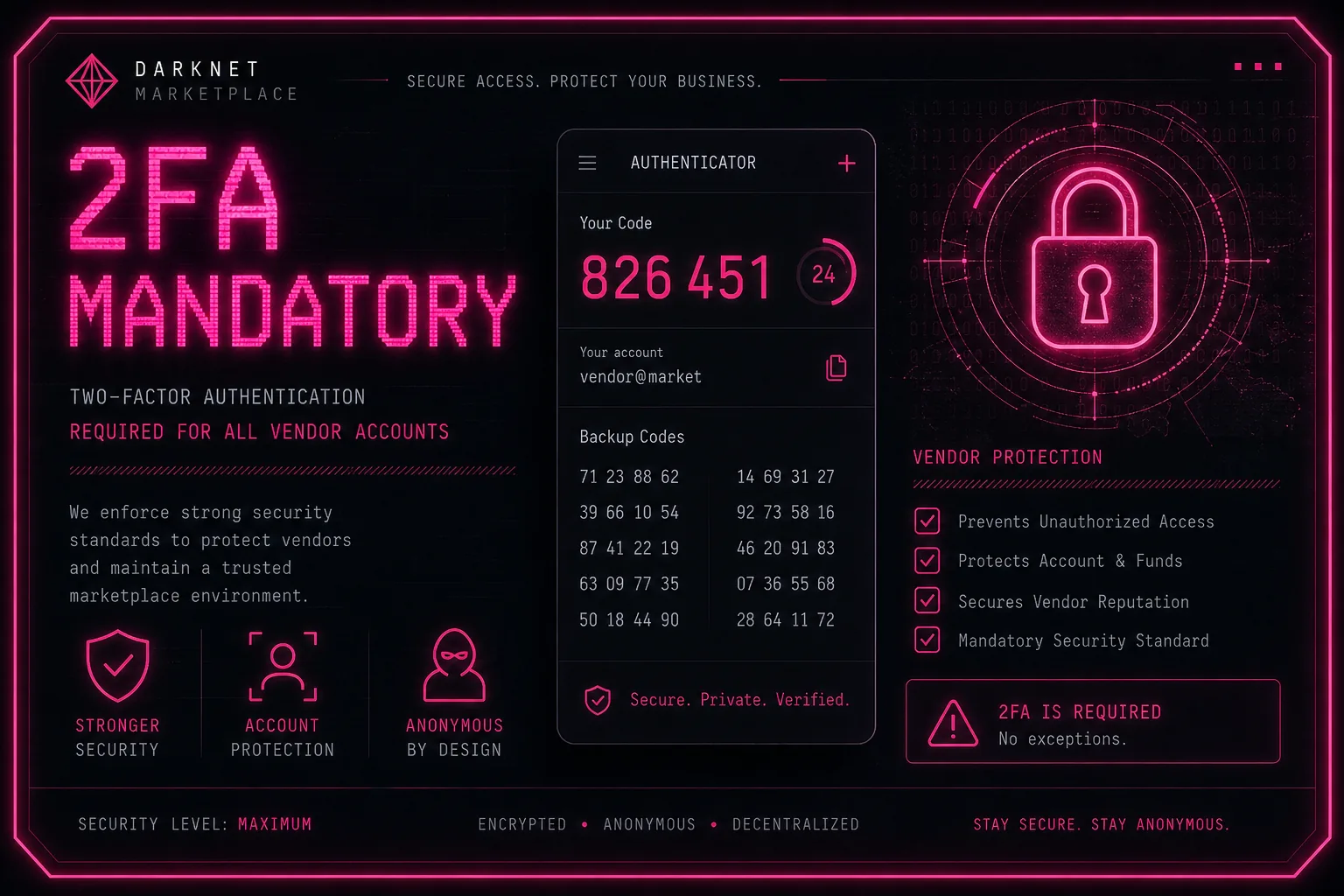
08 — 2FA Enforcement
Two-factor authentication via TOTP (time-based one-time password) is mandatory for all vendor accounts and optional but strongly recommended for buyer accounts. Login anomaly detection flags unusual access patterns automatically.

09 — Harm Reduction Links
Relevant harm reduction documentation is linked directly from product listings in high-risk categories. This reflects a platform-level acknowledgement of user safety obligations, referencing external public health organisations' guidance.
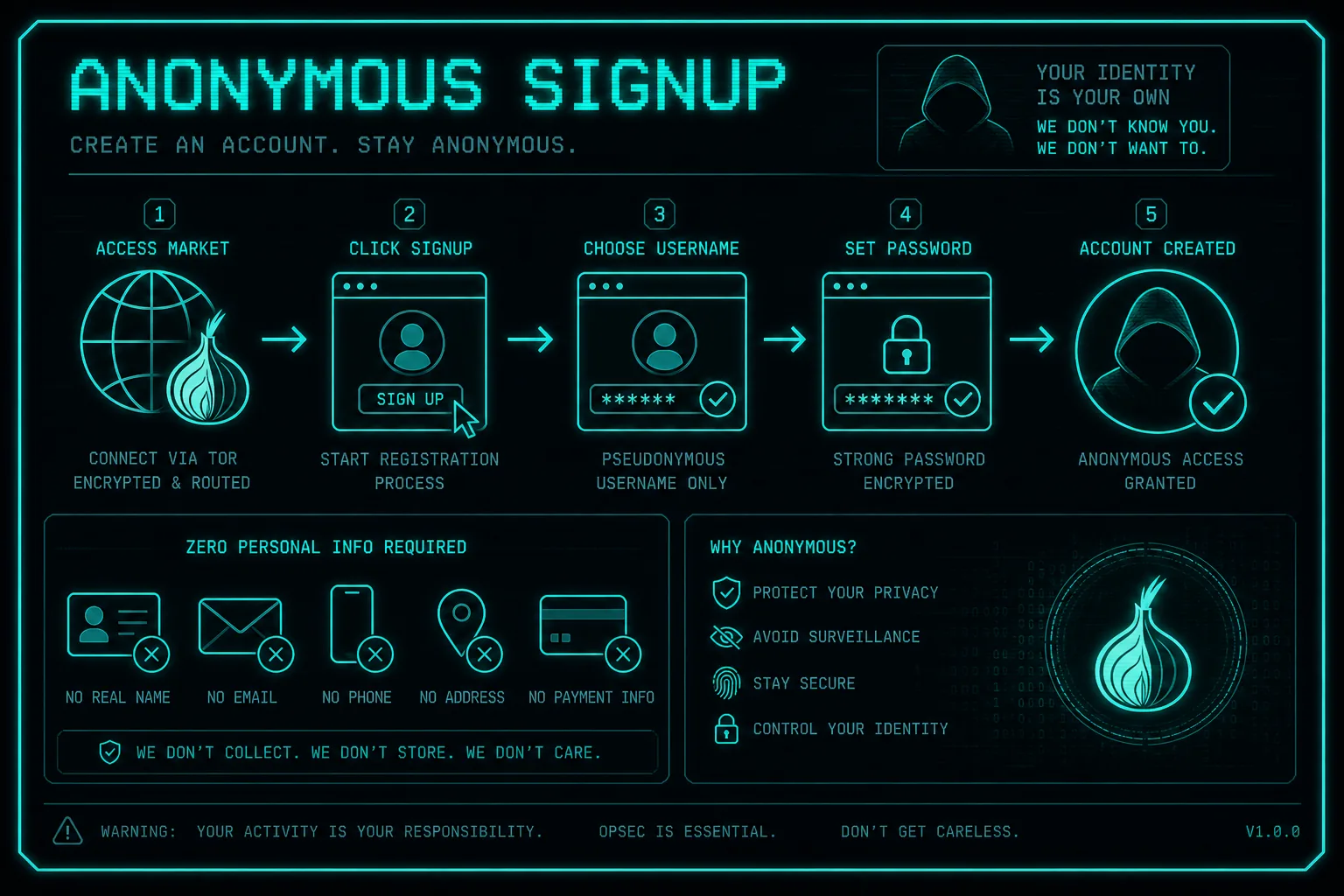
10 — Anonymous Registration
Account creation requires no personally identifiable information. The registration process accepts only a username, PGP key, and security phrase. No email address is required or stored. This minimises any potential data exposure in the event of a server compromise.

11 — Anti-Scam Protocols
Automated pattern detection monitors for common vendor scam behaviours: selective scamming (targeting new buyers), partial delivery fraud, and listing manipulation. High-risk accounts are flagged for manual review before escrow release.
12 — Stealth Guidelines
Vendor listings must comply with platform-defined stealth packaging guidelines before receiving the Verified designation. These guidelines, adapted from community OPSEC research, specify minimum standards for packaging, labelling, and return address practices.
How Does the Escrow System Protect Buyers?
The escrow architecture is the most consequential trust mechanism on any darknet marketplace. Unlike simple centralised escrow — where a platform administrator holds funds and can disappear with them — multi-signature escrow distributes control across multiple cryptographic keys. The Nexus Website documentation describes the escrow flow in detail: funds are sent to a multi-sig address, locked until the buyer confirms delivery, and released only upon a 2-of-3 signature threshold.
Escrow Flow Step-by-Step
- Buyer funds the escrow address after order placement
- Vendor receives order confirmation and ships product
- Buyer marks order received — triggers automatic release
- If dispute raised, moderator key becomes third signature
- Funds release after 2-of-3 parties sign the release transaction
- Finalize early (FE) is available for Trusted Elite vendors only
Escrow Limitations and Buyer Risk
Multi-sig escrow does not eliminate all risk. If a vendor delivers a product that differs from the listing description, proof of discrepancy must be provided to the dispute resolution team. The Nexus Access process itself — using the correct .onion address — is critical: escrow protections only apply on the legitimate platform, not on phishing mirror sites that mimic the interface.
For full crypto guidance including wallet setup and transaction privacy, see the cryptocurrency payment guide.
The Nexus Website maintains documentation accuracy through monthly content review. Market statistics are derived from community-aggregated open-source data and may vary from real-time platform figures.