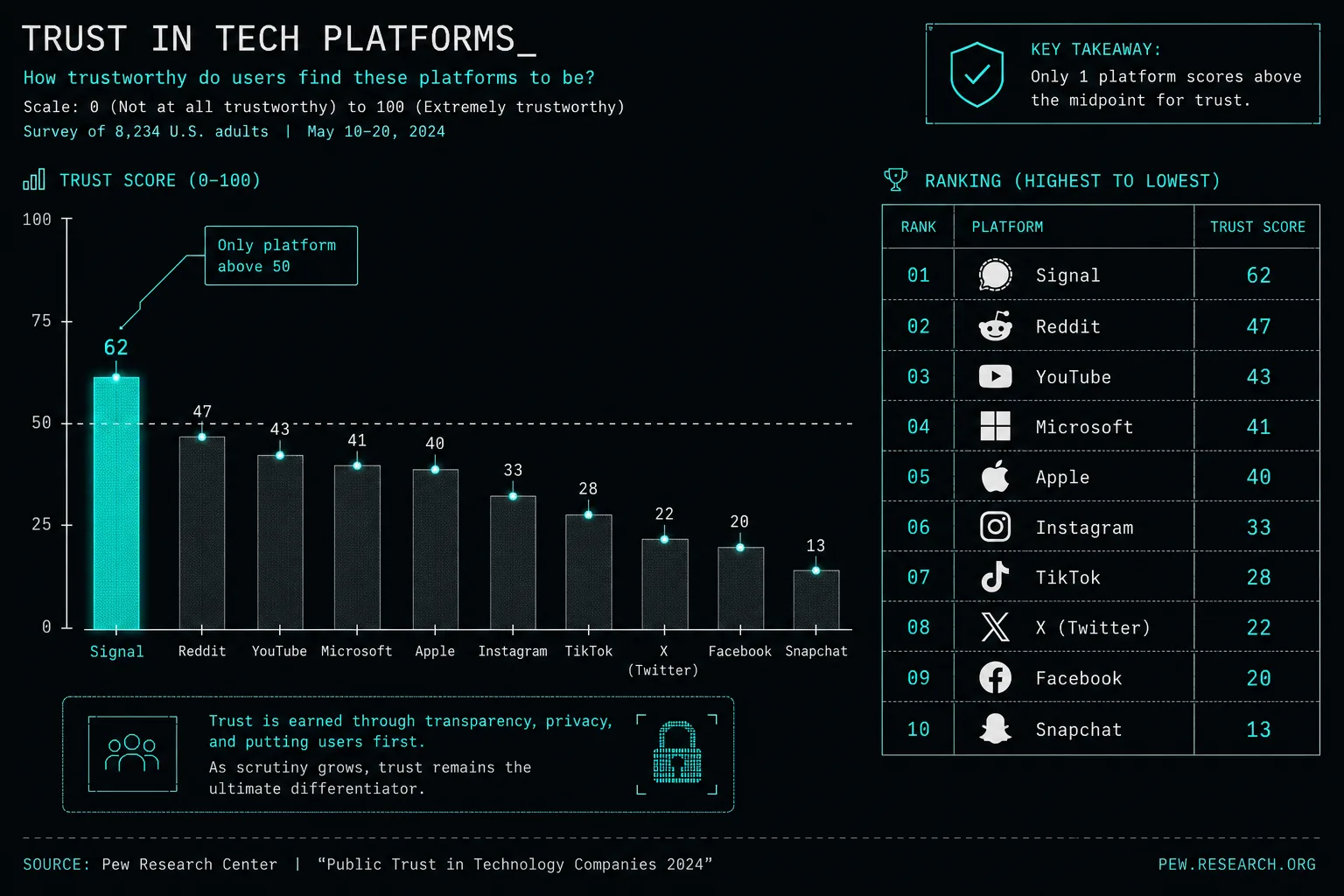
Independent market analysis published in May 2026 placed Nexus at the top of vendor trust scores across active darknet platforms.
Analysis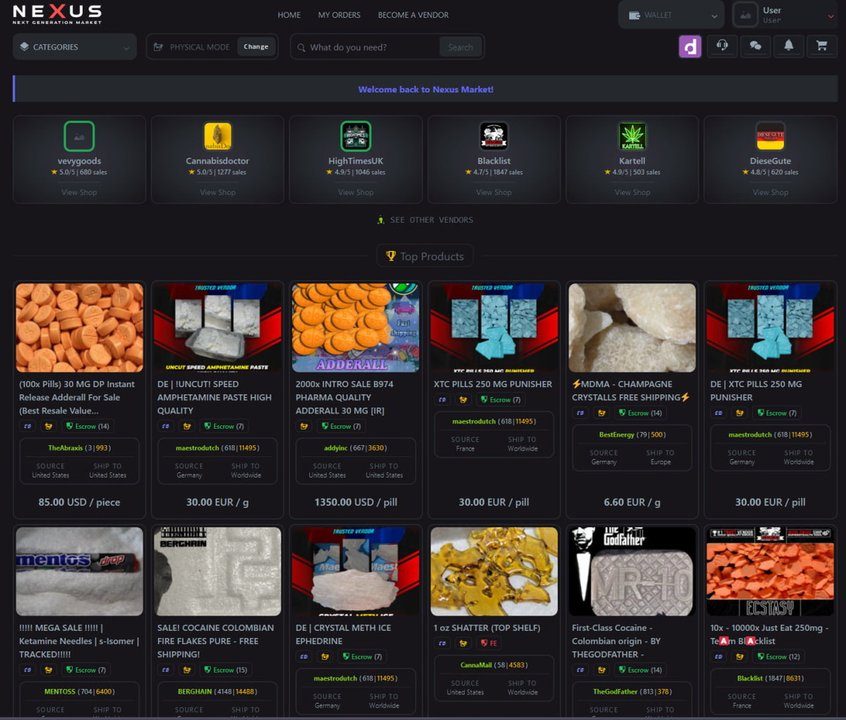
The Nexus Website serves as a comprehensive informational reference for the Nexus darknet marketplace. This resource documents the platform's architecture, vendor verification system, and operational security practices. All content presented here is derived from open-source intelligence and public research. Nothing on this site constitutes legal advice or endorsement of any marketplace activity.
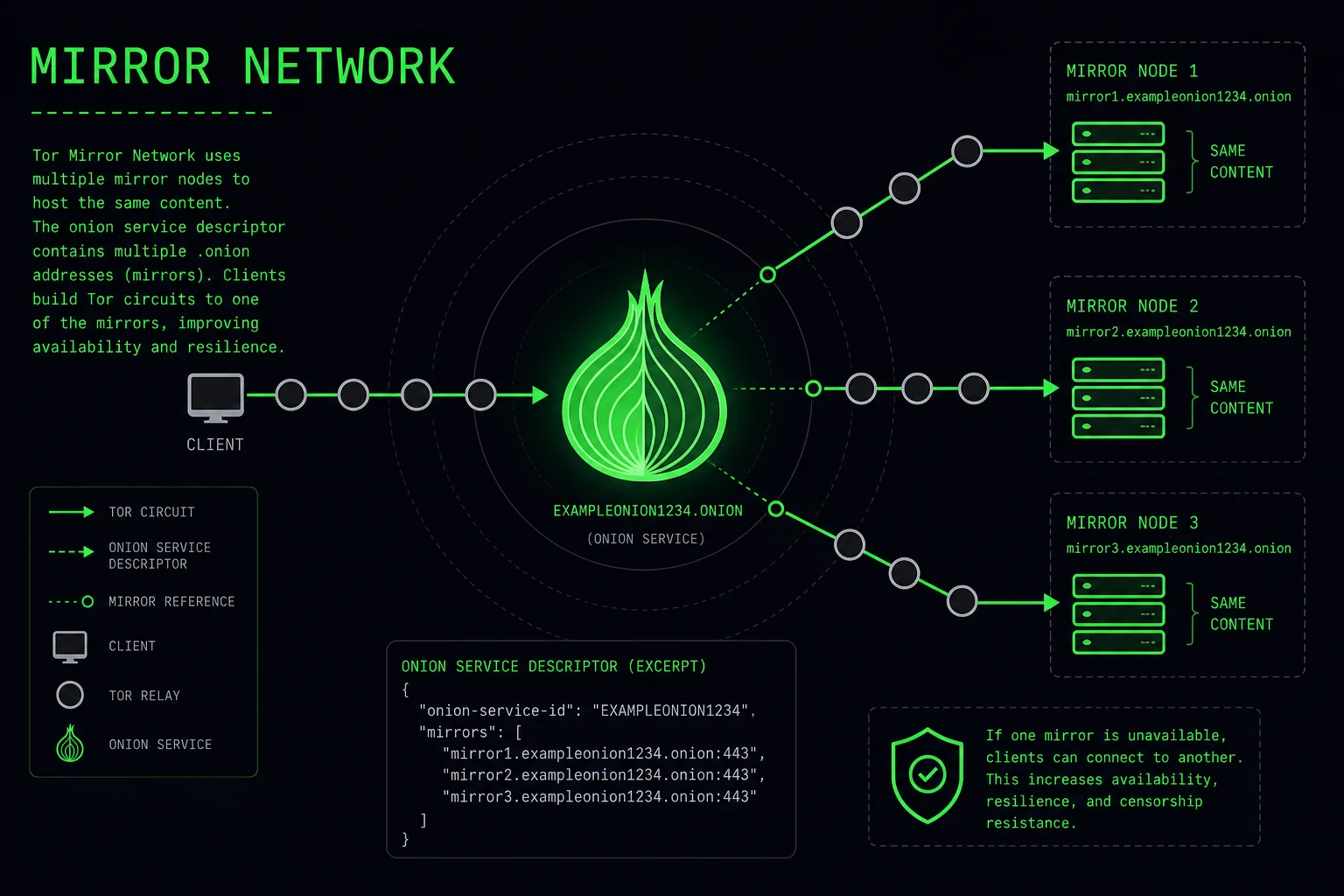
Nexus operates as a decentralised marketplace accessible exclusively through the Tor network. Its infrastructure uses rotating .onion mirror addresses, multi-signature escrow, and PGP-based communication standards. The marketplace has developed a significant vendor base with a reputation-weighted trust system designed to reduce fraud. Researchers and journalists covering digital underground economies frequently reference Nexus as a case study in modern darknet market architecture.
Understanding how the Nexus darknet platform is structured requires examining its foundational technology layers. These six pillars define how the marketplace operates, how vendors are managed, and how buyer transactions are protected. For a deeper breakdown, read the detailed market analysis.
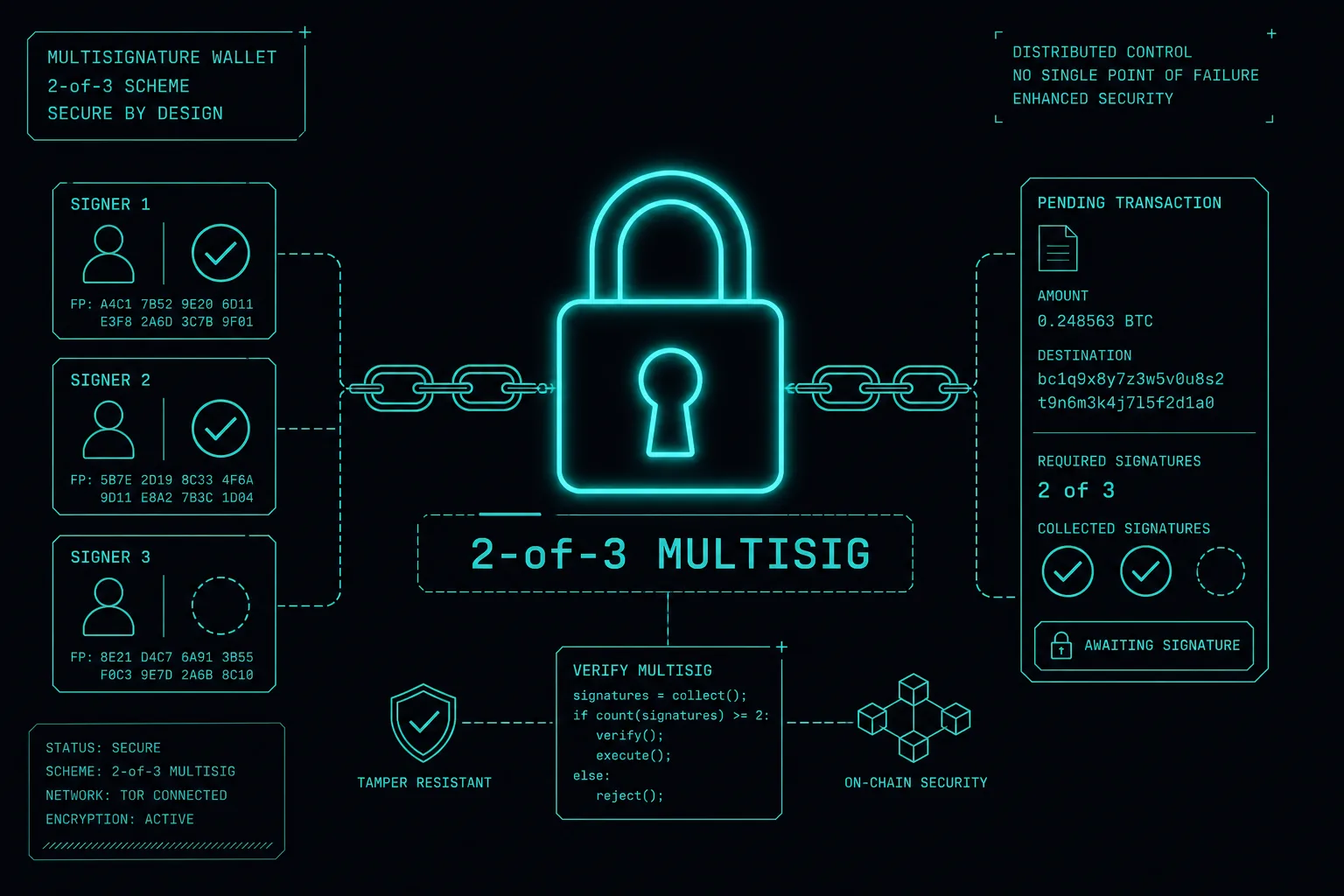
Nexus uses 2-of-3 multi-signature escrow for all transactions. Funds are not released until the buyer confirms receipt, and neither party can unilaterally access them without dispute resolution involvement.

All vendors on Nexus submit to a verification process involving identity bonding, PGP key registration, and tiered trust levels. Buyer reviews are cryptographically signed to prevent manipulation.
The platform maintains multiple rotating .onion addresses to ensure continuous availability. Mirror links are updated every 72 hours to counteract network disruptions and potential takedown attempts.
Nexus employs a trained moderation team for escrow disputes. Cases are resolved based on order evidence, communication logs, and vendor history. Median resolution time is under 24 hours.
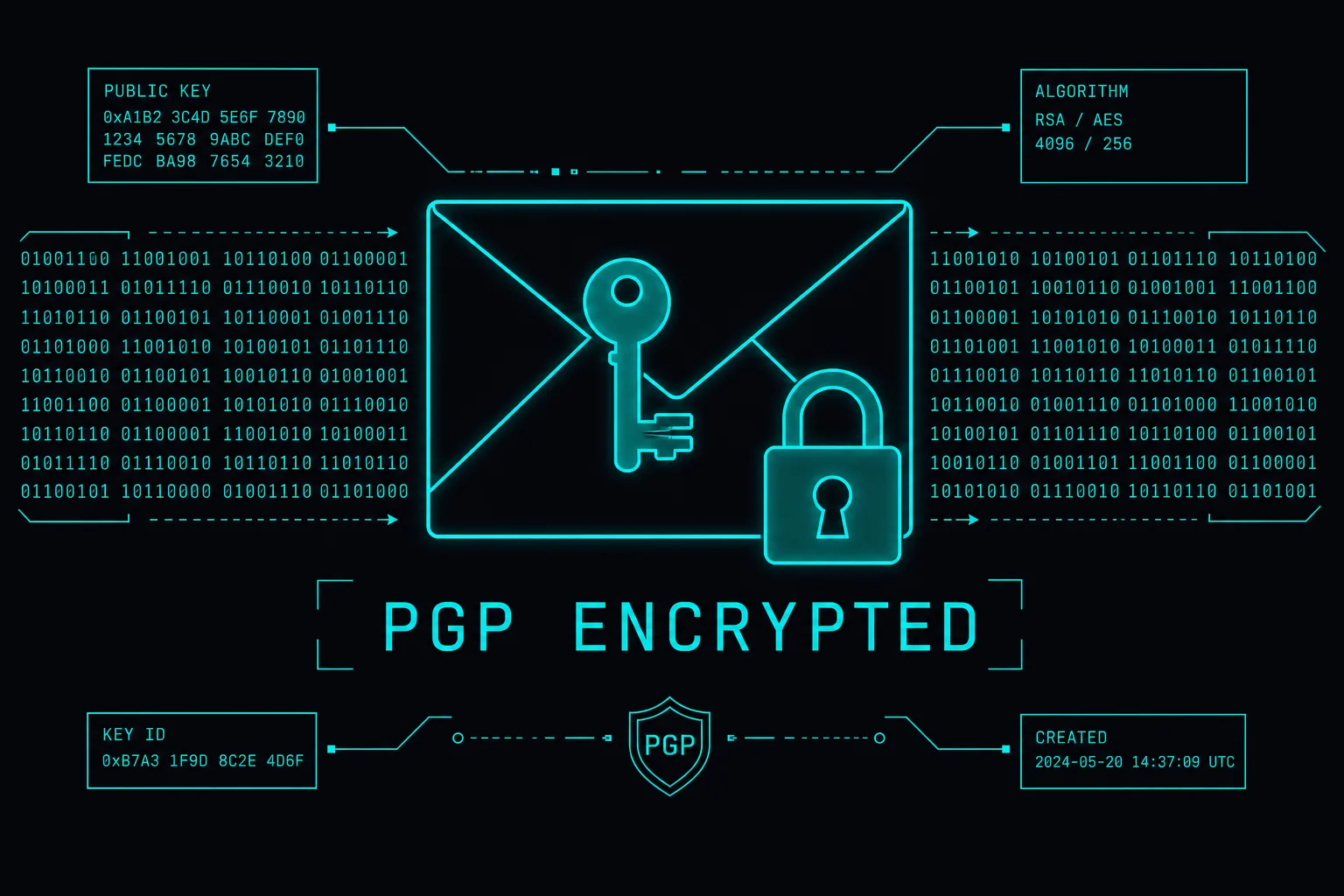
End-to-end PGP encryption is the enforced standard for all vendor-buyer communications on Nexus. Public keys are displayed on vendor profiles and verified at account creation to prevent impersonation.
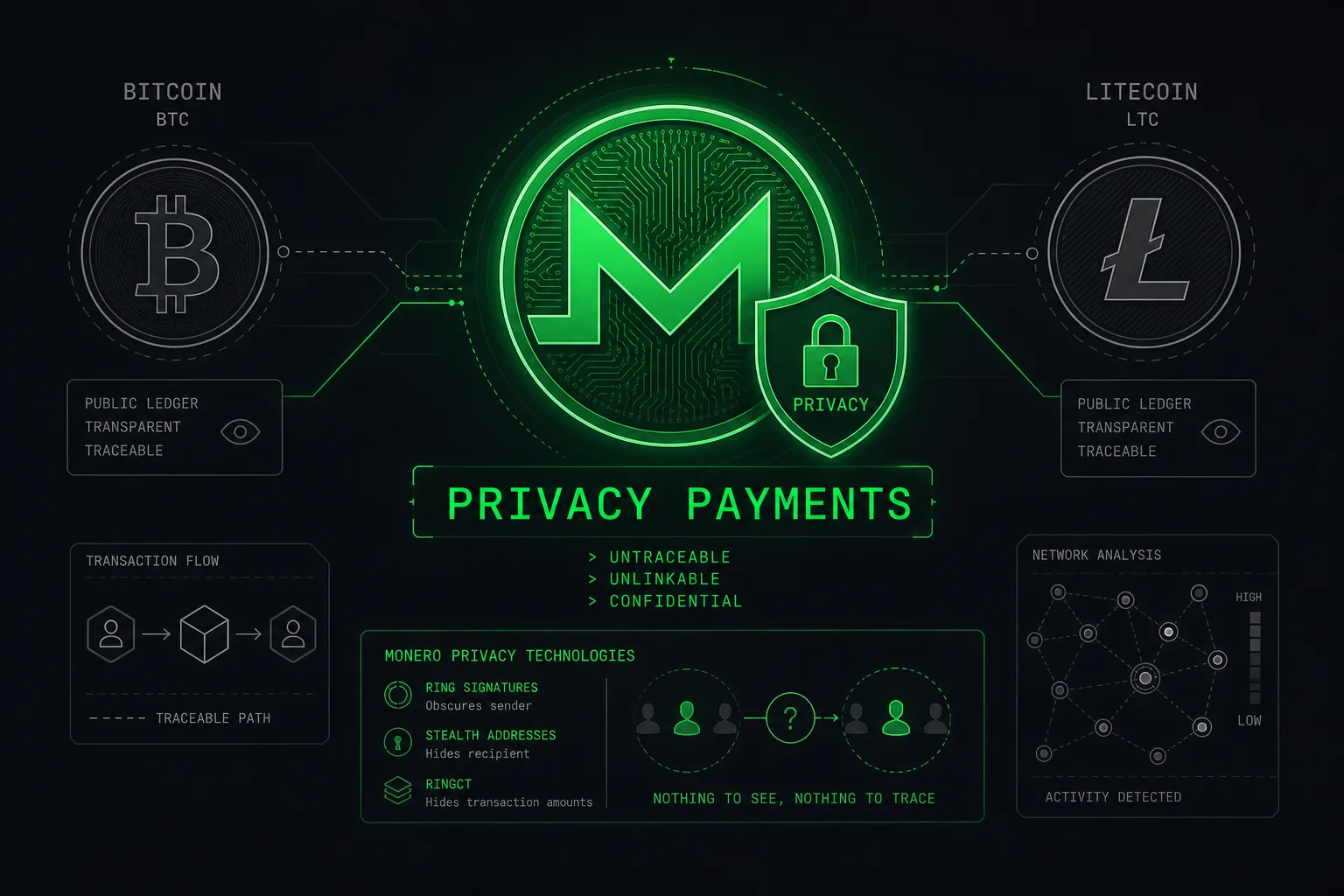
Bitcoin, Litecoin, and Monero are natively supported. Monero is the recommended payment method due to its built-in ring signature and stealth address architecture, providing transaction-level privacy by default.
The Nexus Verified designation is assigned to vendors who have completed the platform's full authentication pipeline. This involves submitting a bonding deposit, providing a PGP-signed application, and maintaining a dispute-free order history above a minimum transaction threshold. Verified vendors receive a badge visible on all listings and access to extended escrow windows.
Nexus accepts three cryptocurrencies: Bitcoin (BTC), Litecoin (LTC), and Monero (XMR). Each presents different privacy and speed trade-offs. The platform's internal documentation recommends XMR for all privacy-sensitive transactions, citing its ring signature protocol as significantly harder to trace than Bitcoin's transparent ledger.
For detailed guidance on each currency's privacy characteristics, visit the cryptocurrency payment guide.
The following summaries cover publicly reported developments in darknet marketplace operations, privacy technology, and platform security. Full articles are available in the news archive.
Independent market analysis published in May 2026 placed Nexus at the top of vendor trust scores across active darknet platforms.
Analysis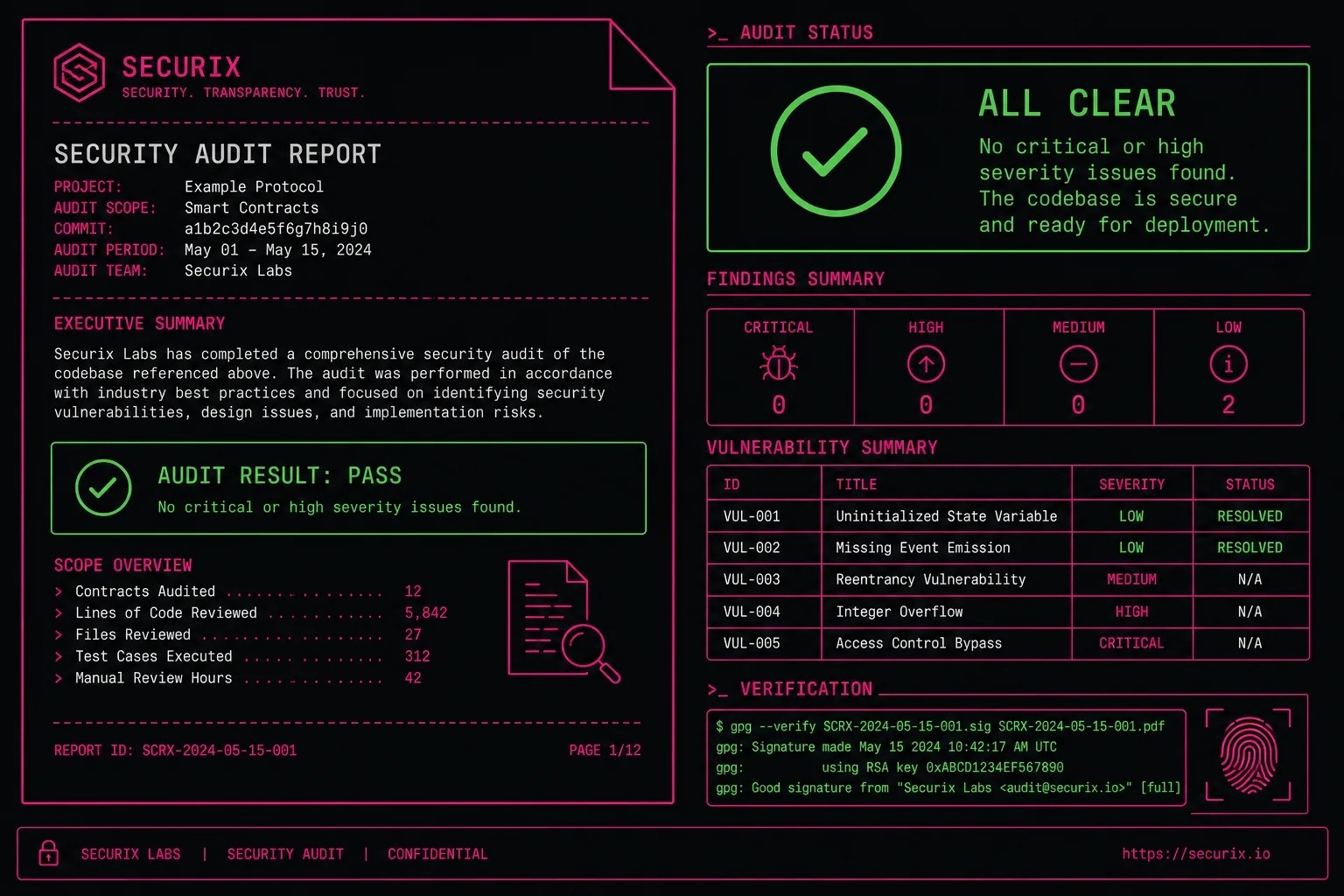
The third-party security review confirmed no critical vulnerabilities in Nexus's escrow infrastructure during the audit period.
Security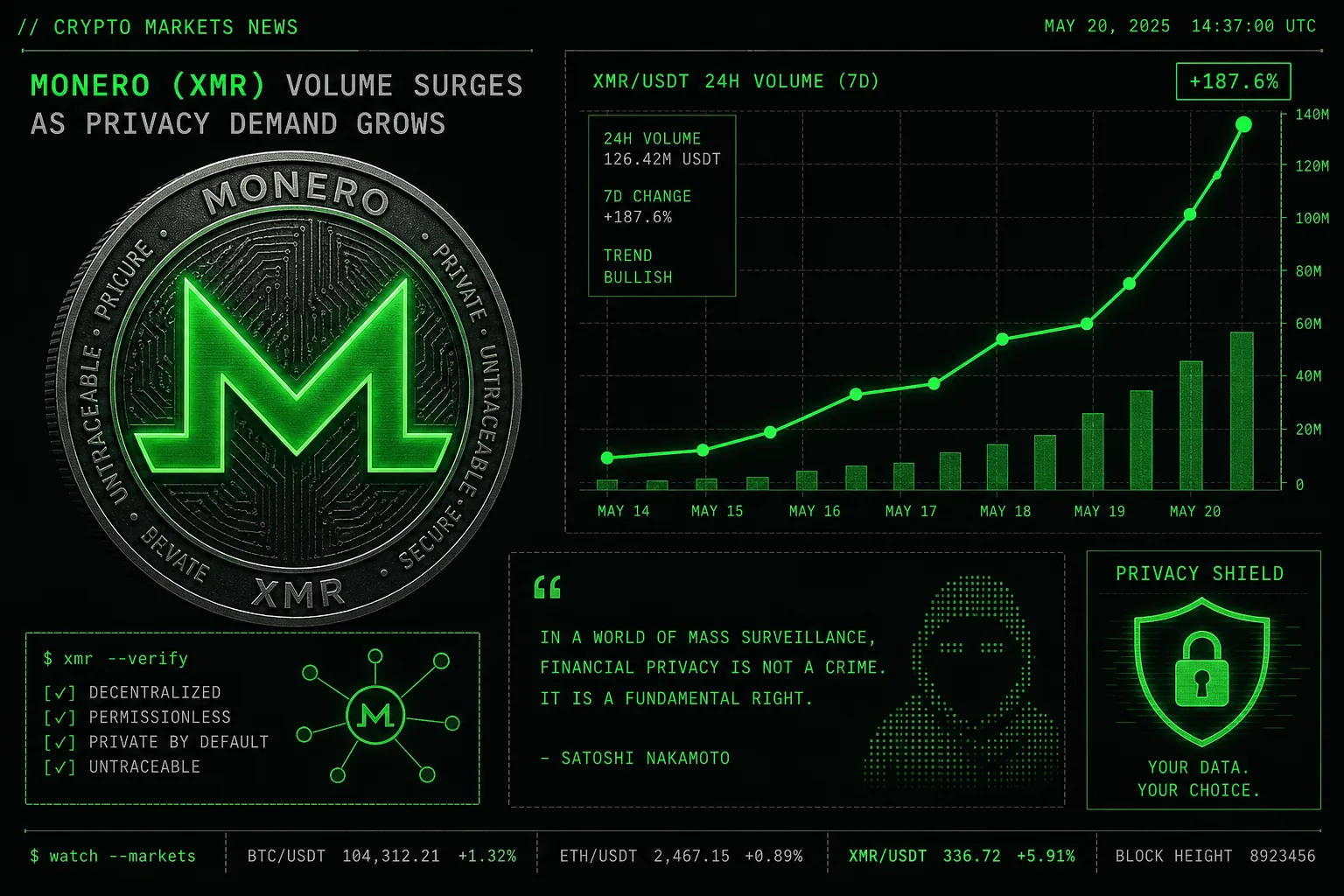
Monero transaction volumes on darknet platforms rose by 34% in Q1 2026, driven by user migration from transparent blockchains.
Crypto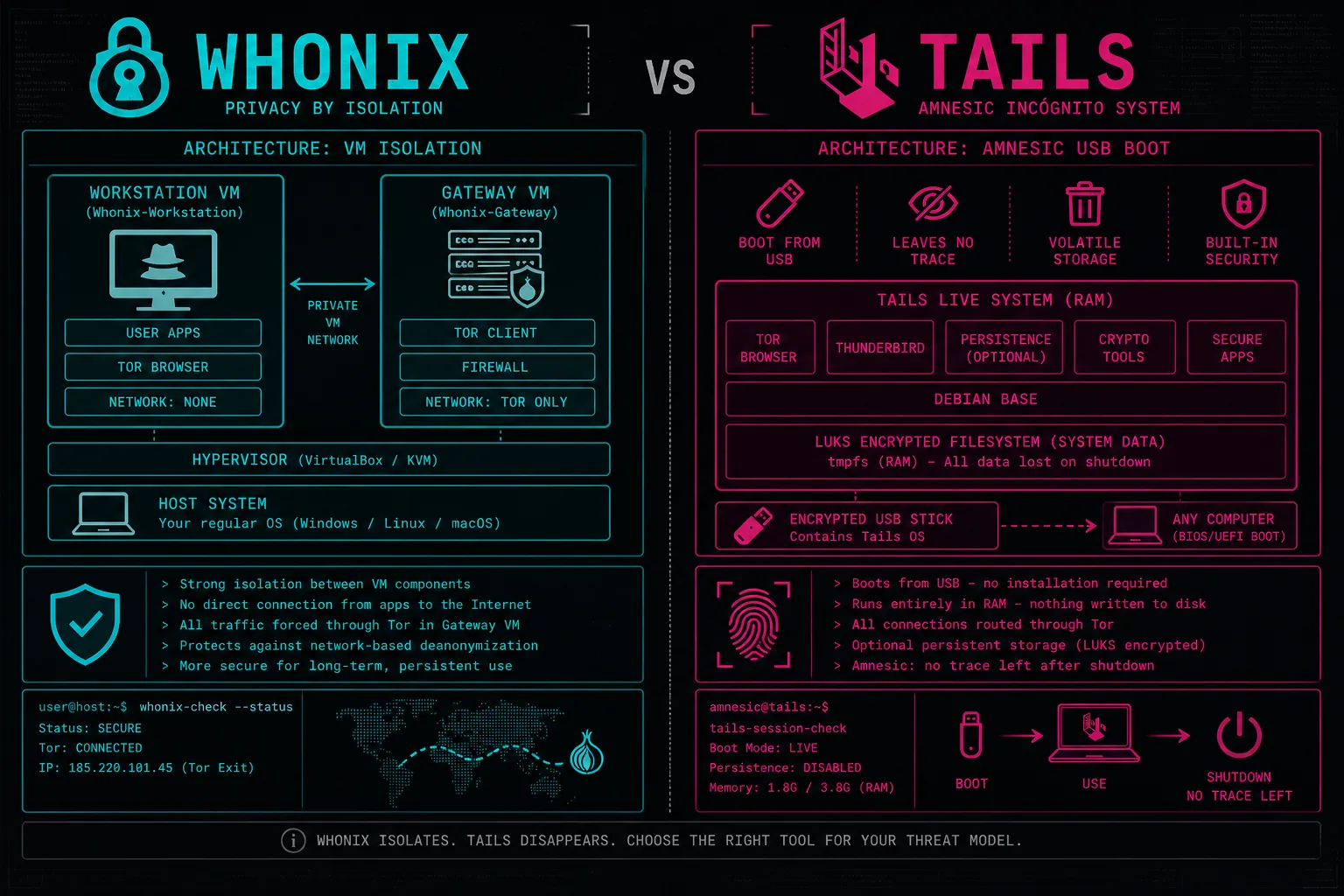
A comprehensive technical review examines both operating systems' threat models, persistence options, and real-world use cases.
OPSEC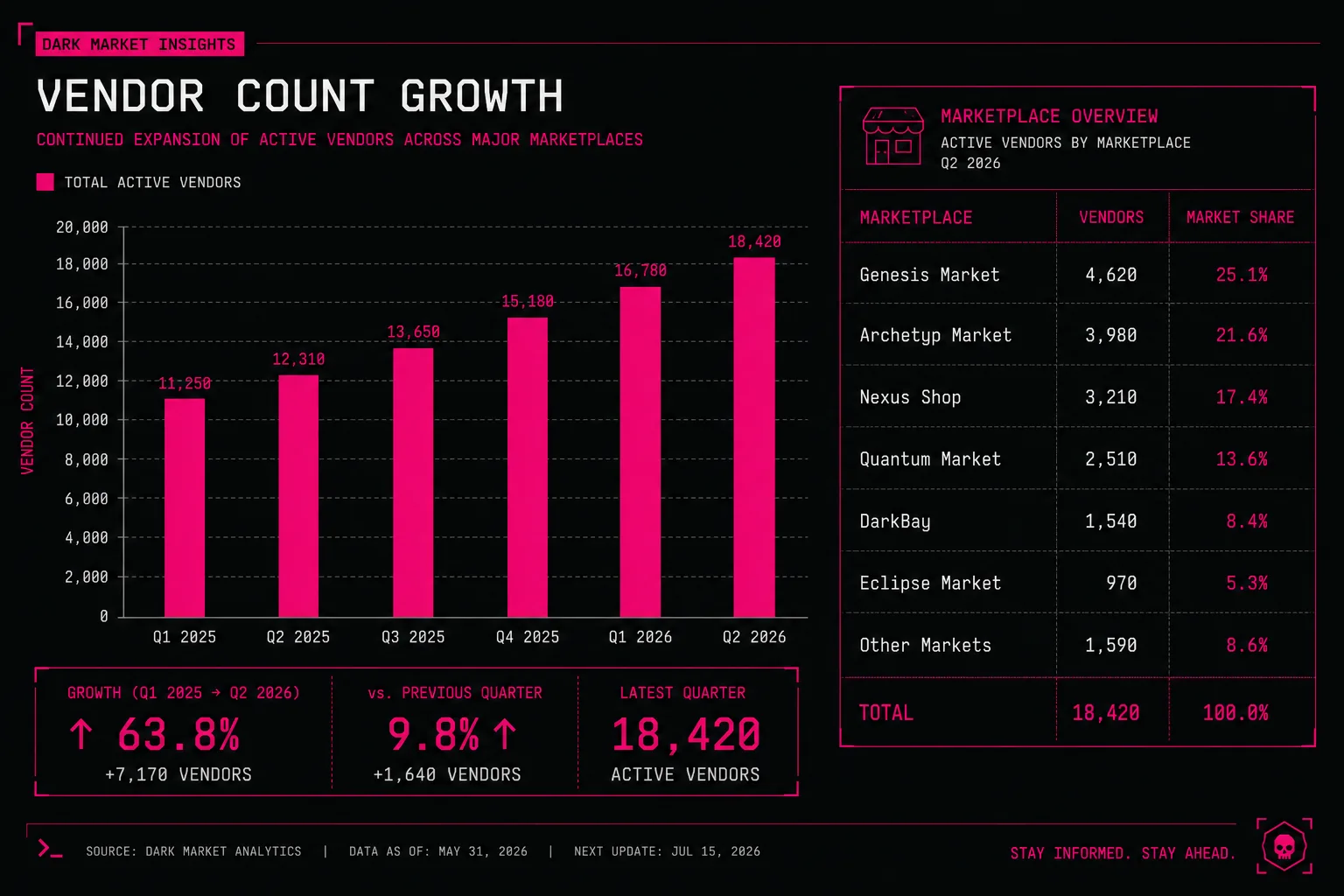
Platform statistics for Q1 2026 show 2,847 active vendors — the highest figure recorded since the platform's launch.
Statistics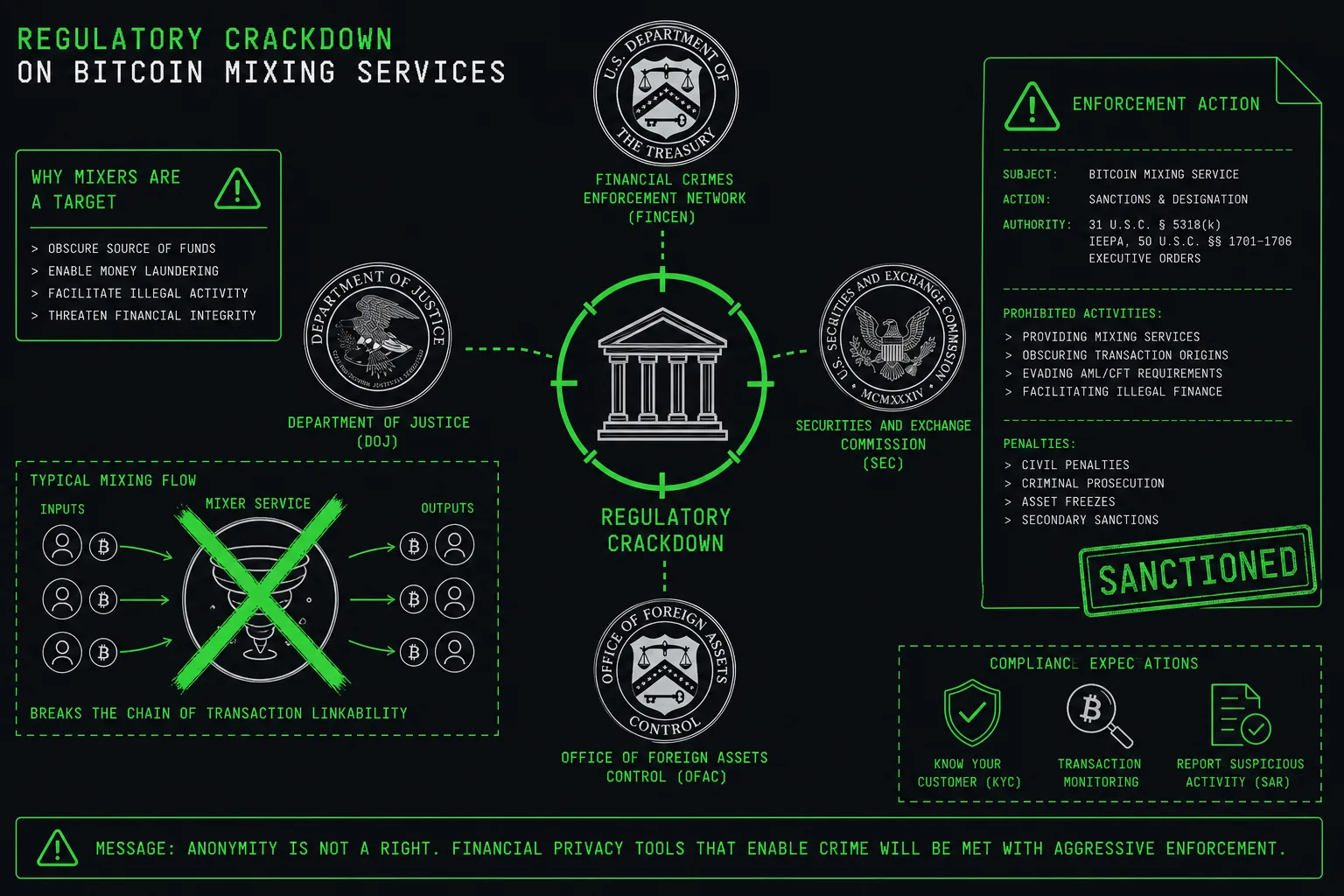
International financial regulators expanded guidance on cryptocurrency tumbling services, impacting transaction privacy options.
Crypto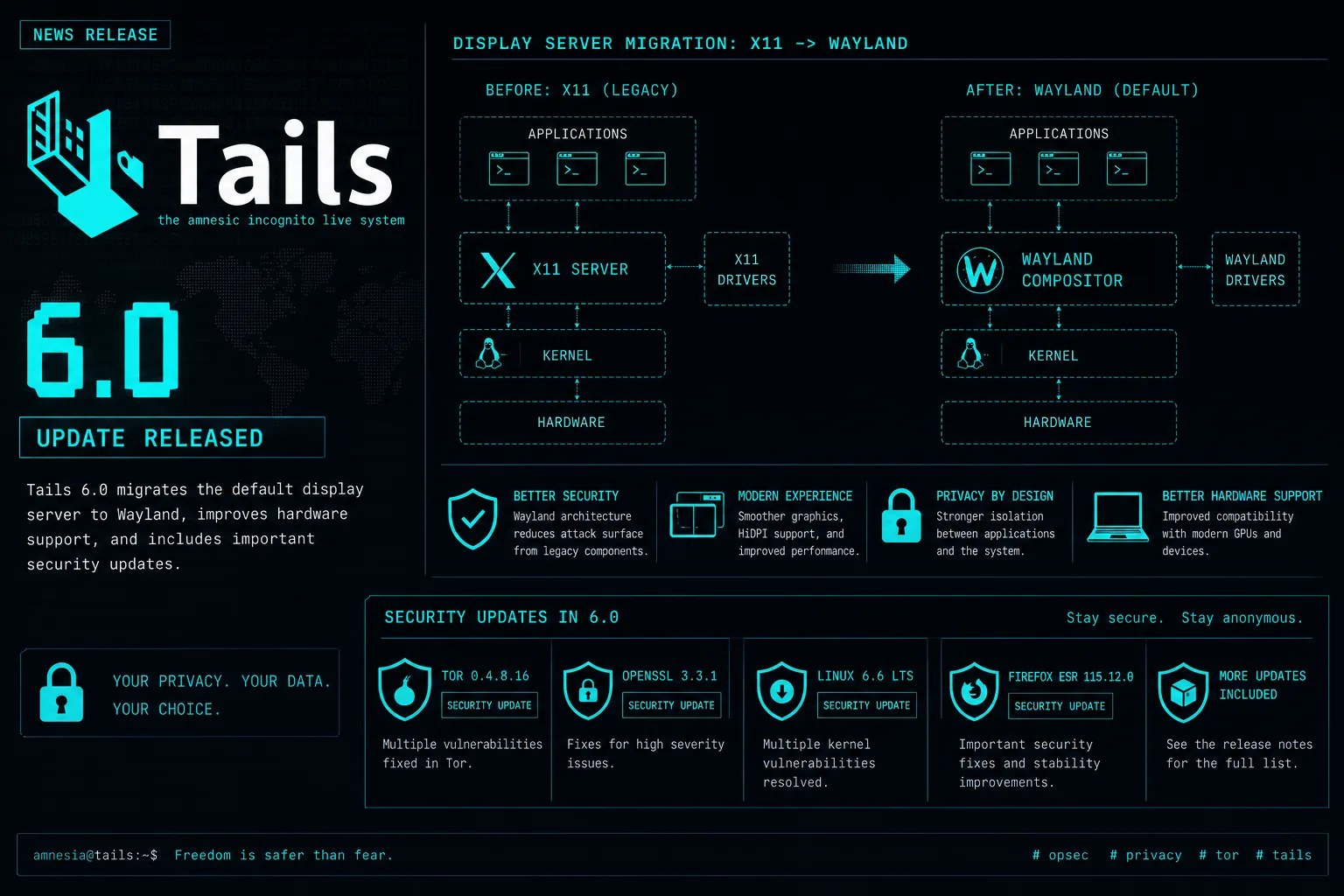
The updated Tails release introduced Wayland compositing and improved hardware support, enhancing usability for privacy-sensitive environments.
Privacy Tools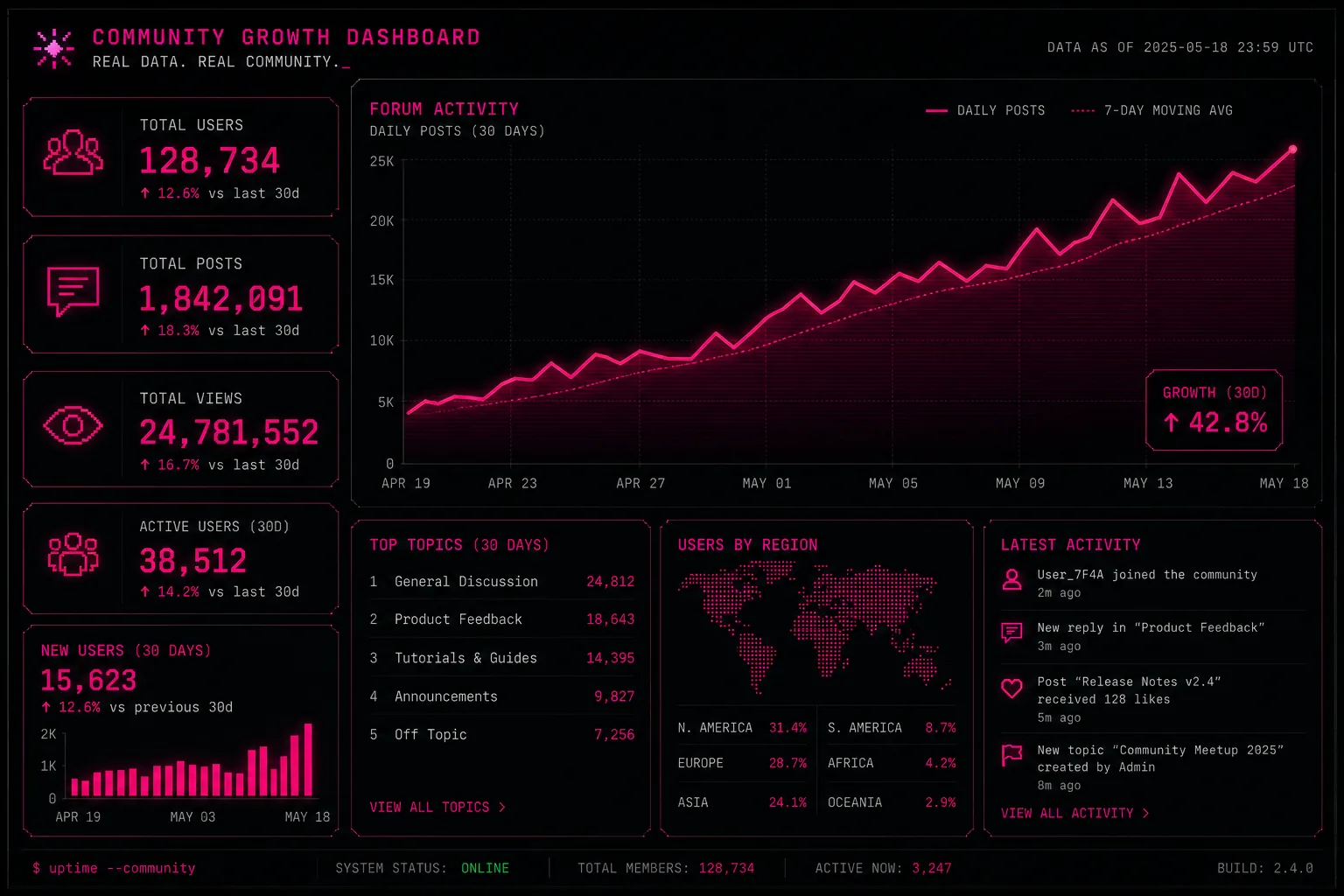
Community-sourced data aggregated across forums shows consistent month-on-month user growth across Nexus platform registrations.
Community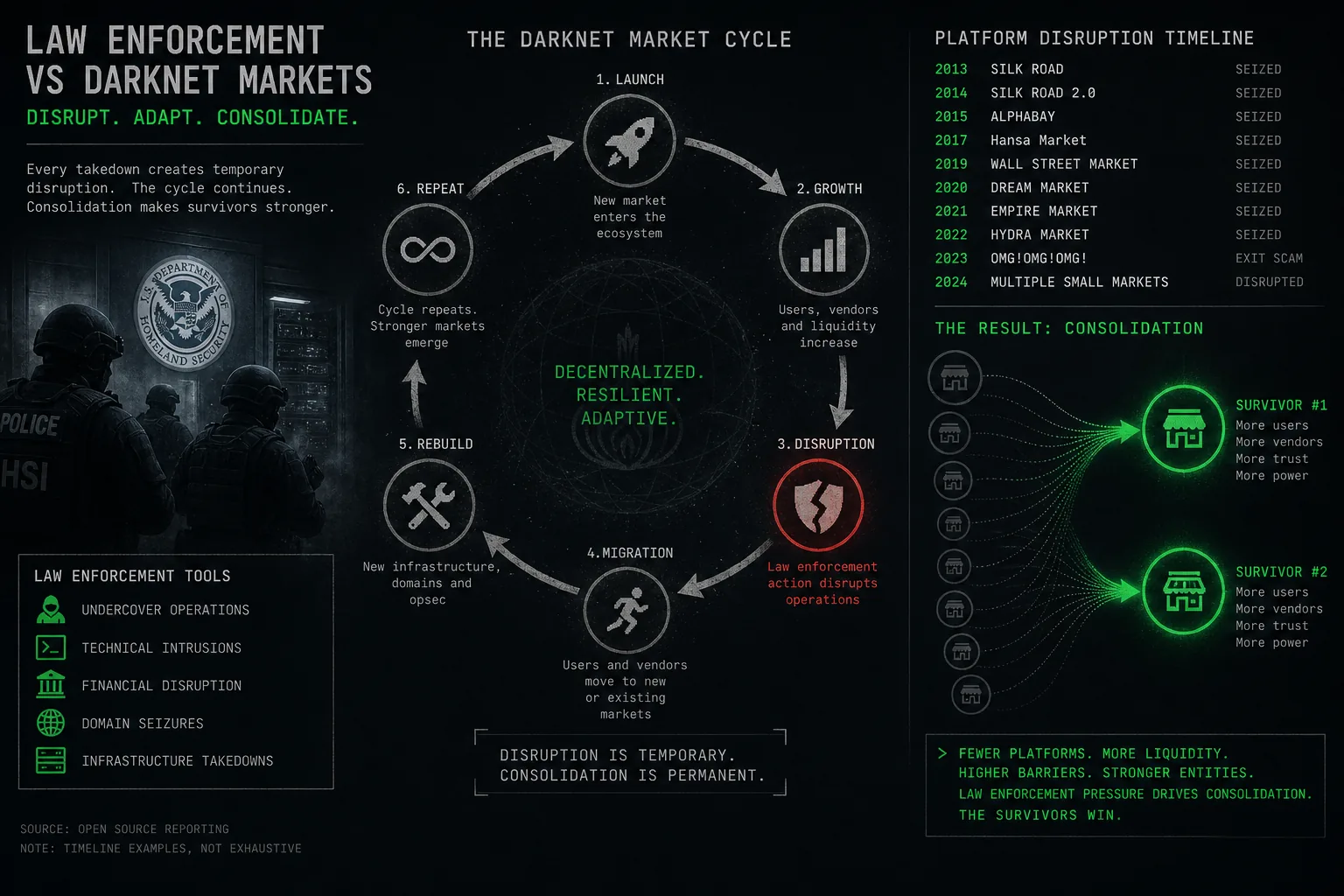
Year-end analysis documents how coordinated agency actions in late 2025 drove consolidation, with Nexus emerging as the dominant active platform.
AnalysisHarm reduction is a public health framework that prioritises practical risk minimisation over abstinence-only approaches. The Nexus platform links harm reduction documentation directly from product listings. This section summarises the most critical principles — the full guide is at the harm reduction resource page.
Opioid overdose signs include unresponsiveness, slow or absent breathing, blue-tinted lips, and pinpoint pupils. Stimulant overdose presents as chest pain, seizures, or extreme hyperthermia. For any suspected overdose, call emergency services immediately regardless of legal circumstances — Good Samaritan laws protect callers in most jurisdictions.
Operational security (OPSEC) refers to the process of protecting individually unclassified information that could be combined to reveal sensitive details about identity or activity. Nexus Access should always be performed within a properly configured anonymity stack. The documentation on this Nexus Website covers OPSEC extensively — see the complete OPSEC guide for tools and threat models.
Traffic analysis, timing correlation, and metadata harvesting are primary de-anonymisation vectors on darknet platforms. Without a complete OPSEC framework, even technically sound tools can be undermined by behavioural patterns. Researchers documenting market activity face the same exposure risks as ordinary users.
Most de-anonymisation incidents trace back to behavioural errors rather than cryptographic failures. Reusing usernames across platforms, using personal email addresses for registrations, and disabling Tor's security settings are among the most frequently documented mistakes in published law enforcement case studies.
Phishing represents the most prevalent attack vector targeting darknet market users. Fake mirror sites, forum posts with counterfeit links, and social engineering via messaging platforms account for the majority of credential theft incidents documented in open-source intelligence reporting.
Fake Nexus mirrors typically copy the visual interface precisely. The only reliable verification method is confirming the full v3 .onion address matches a known legitimate source. Always cross-reference with the PGP-signed address list. The full anti-phishing guide covers advanced verification techniques, browser security settings, and case studies of documented phishing campaigns.
The following answers address common informational queries about the Nexus platform, its operational structure, and safe access practices.
For a full expanded FAQ, visit the dedicated FAQ page.
This Nexus Website maintains a commitment to accurate, source-verified, and legally compliant documentation. All information is presented without commercial intent, affiliate relationships, or promotional objectives. Readers are encouraged to cross-reference all claims with independent sources and to consult legal counsel regarding their jurisdiction's applicable laws before engaging with any darknet platform.
Daily fact: Loading...