Whonix vs Tails: Anonymity Tool Comparison 2026
A technical comparison published in March 2026 by independent security researchers evaluated Whonix and Tails OS as the two most widely documented anonymity operating systems for darknet access. The comparison covered architecture differences, threat model alignment, hardware compatibility, and specific use case scenarios. Both tools are referenced in the Nexus Website OPSEC documentation.
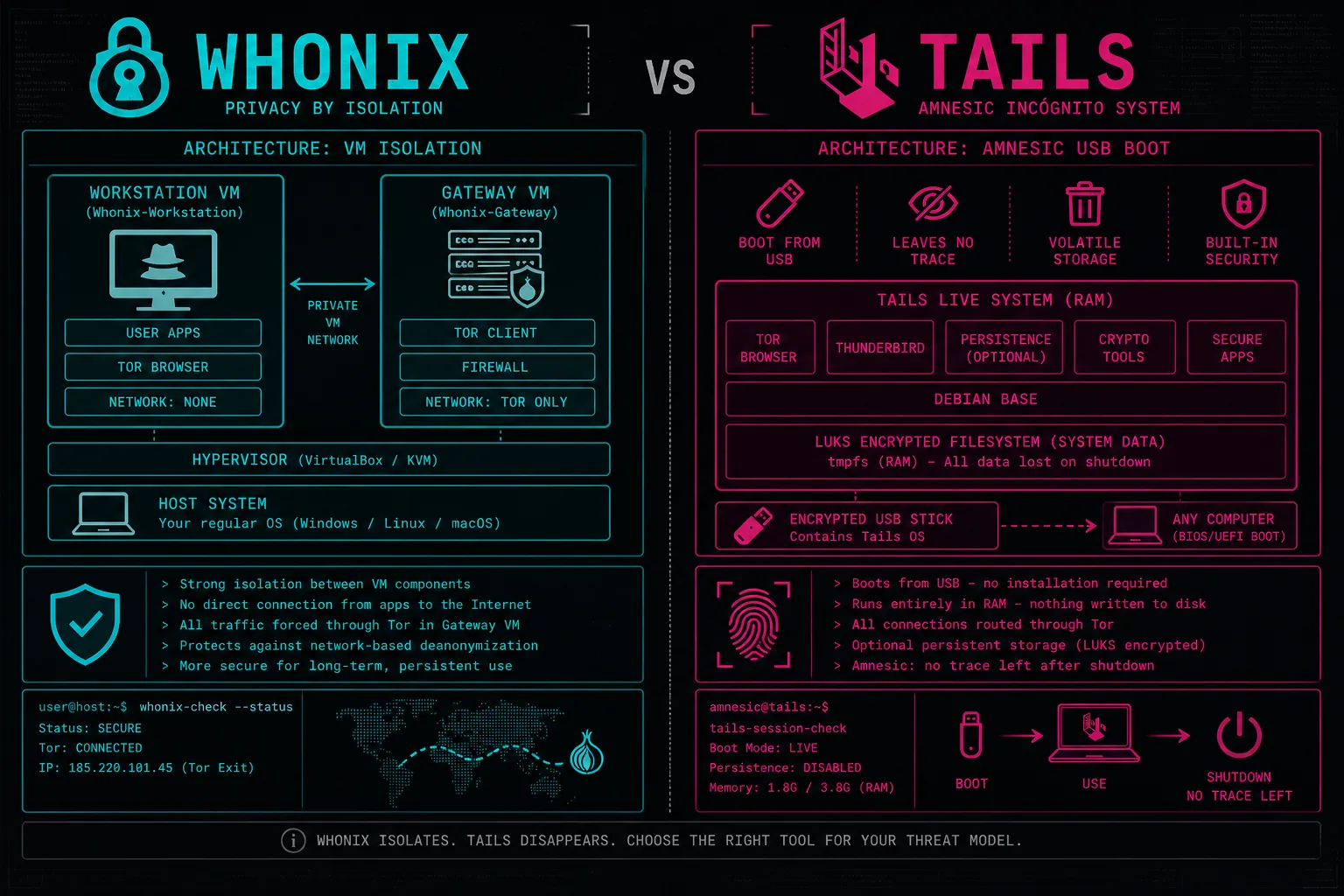
How Do Whonix and Tails Differ in Architecture?
Tails OS is an amnesic live OS booted from USB that routes all network traffic through Tor automatically and leaves no trace on the host machine when the session ends. Whonix operates as two virtual machines: a Gateway VM routing all traffic through Tor, and an isolated Workstation VM that supports persistent storage. Unlike Tails, Whonix is suitable for ongoing use requiring data retention between sessions.
Which Tool Is Better for Nexus Access?
Both tools provide equivalent Tor network anonymity for Nexus Access. The choice depends on threat model: Tails for maximum amnesia, Whonix for persistent workflows. Whonix provides an additional property: even if the Workstation VM is compromised, the real IP cannot leak because the Workstation has no direct internet connection. Neither tool protects against ISP-level traffic correlation or hardware firmware surveillance. Full documentation is in the Nexus Website OPSEC guide.
What Are the Limitations of Each Approach?
Related: Market Overview · OPSEC Guide · Crypto Guide · News Archive · Official Access Links