OPSEC Research: Common De-Anonymisation Mistakes
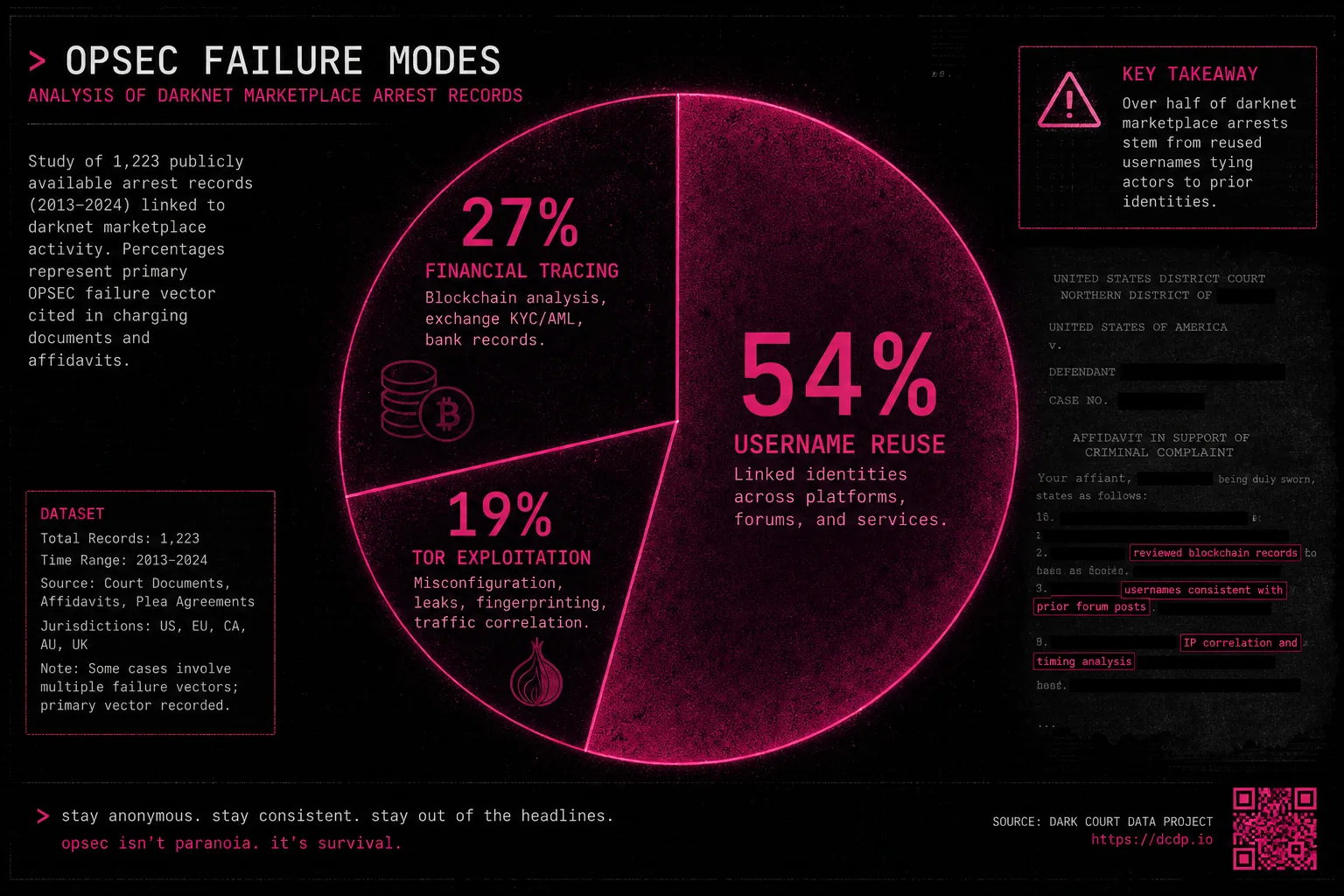
Researchers affiliated with a digital civil liberties organisation published an analysis in October 2025 of 87 publicly available arrest affidavits related to darknet marketplace activity from 2020 to 2025. The study identified the most common operational security failures leading to de-anonymisation. The findings represent one of the most systematic open-source analyses of darknet OPSEC failure modes from public court records.
What Did the Arrest Affidavit Analysis Find?
Username reuse was identified as a contributing factor in 61 percent of reviewed cases, making it the single most common de-anonymisation vector. The second most common factor (43 percent) was financial tracing through KYC cryptocurrency exchanges. Monero was mentioned in financial evidence sections of fewer than 4 percent of affidavits, consistent with XMR's resistance to standard chain analysis techniques used by Chainalysis and similar firms.
What Were the Most Common OPSEC Failures?
Technical de-anonymisation through Tor exploitation or traffic correlation was identified in only 6 percent of cases. The data suggests most impactful risk mitigation steps are behavioural rather than technical: never reuse usernames, never use KYC exchanges, never ship to identifiable addresses. Tor Browser and Tails OS protect against the minority of cases involving network surveillance but are ineffective against social and financial mistakes causing the majority of documented de-anonymisations.
How Can These Mistakes Be Avoided?
Related: Market Overview · OPSEC Guide · Crypto Guide · News Archive · Official Access Links